Cisco Asdm 7.2 For Asa 5510
- Cisco Security Appliance Command Line Configuration Guide ...
- Solved: Cisco ASA 5510 And ASDM. - Cisco Community
- See More Results
- Cisco Asdm 7.2 For Asa 55104
- Cisco Asdm 7.2 For Asa 5510 Software
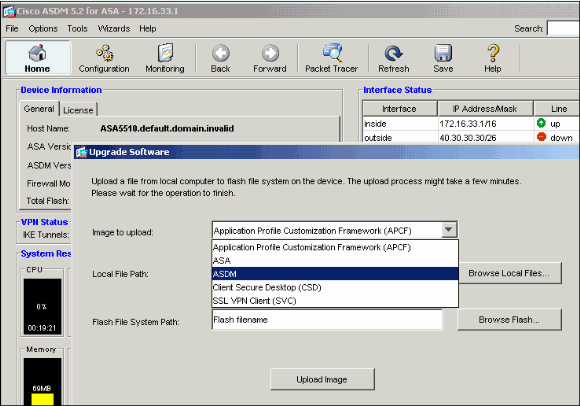
- Cisco Adaptive Security Device Manager (ASDM)
- Cisco Asdm 7.2 For Asa 5510 Driver
Apr 28, 2021 Cisco Details: Cisco ASDM-IDM Launcher v1.6(0) Cisco ASDM 7.4(1) for ASA. Cisco ASA Version: 9.1(6) Cisco ASA Device Type: ASA 5510. For anyone who comes looking for these solutions, it is important to understand the IT system security implications involved. Aug 18, 2015 This configuration can also be used with these Cisco products: Cisco ASA Versions 9.1(5) and later. Cisco ASDM Version 7.2.1. Background Information. The packet capture process is useful when you troubleshoot connectivity problems or monitor suspicious activity. Again, Cisco product is unlike those home user edition Cisco linksys router, this box is not designed for home user to “play”, so user has to do “more work” to go into it’s sweet ASA ASDM. ASA5505 is running on FOS version 7.2, the command line is slightly different from IOS command.
Introduction
This document describes how to configure the Cisco Adaptive Security Appliance (ASA) Next-Generation Firewall in order to capture the desired packets with either the Cisco Adaptive Security Device Manager (ASDM) or the CLI.
Prerequisites
Requirements
This document assumes that the ASA is fully operational and is configured in order to allow the Cisco ASDM or the CLI to make configuration changes.
Components Used
This document is not restricted to specific hardware or software versions.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Related Products
This configuration can also be used with these Cisco products:
Cisco ASA Versions 9.1(5) and later
Cisco ASDM Version 7.2.1
Background Information
The packet capture process is useful when you troubleshoot connectivity problems or monitor suspicious activity. In addition, you can create multiple captures in order to analyze different types of traffic on multiple interfaces.
Configure
This section provides information that you can use in order to configure the packet capture features that are described in this document.
Note: Use the Command Lookup Tool (registered customers only) in order to obtain more information on the commands used in this section.
Network Diagram
This document uses this network setup:
Configurations
Note: The IP addressing schemes that are used in this configuration are not legally routable on the Internet. They are RFC 1918 addresses that are used in a lab environment.
Configure Packet Capture with the ASDM
Note: This example configuration is used in order to capture the packets that are transmitted during a ping from User1 (inside network) to Router1 (outside network).
Complete these steps in order to configure the packet capture feature on the ASA with the ASDM:
- Navigate to Wizards > Packet Capture Wizard in order to start the packet capture configuration, as shown:
- The Capture Wizard opens. Click Next.
- In the new window, provide the parameters that are used in order to capture the INGRESS traffic. Select inside for the Ingress Interface and provide the source and the destination IP addresses of the packets to be captured, along with their subnet mask, in the respective space provided. Also, choose the packet type to be captured by the ASA (IP is the packet type chosen here), as shown:
Click Next. - Select outside for the Egress Interface and provide the source and the destination IP addresses, along with their subnet mask, in the respective spaces provided. If Network Address Translation (NAT) is performed on the Firewall, take this into consideration as well.
Click Next. - Enter the appropriate Packet Size and the Buffer Size in the respective space provided, as this data is required in order for the capture to take place. Also, remember to check the Use circular buffer check box if you want to use the circular buffer option. Circular buffers never fill up. As the buffer reaches its maximum size, older data is discarded and the capture continues. In this example, circular buffer is not used, so the check box is not checked.
Click Next. - This window shows the Access-lists that must be configured on the ASA so that the desired packets are captured, and it shows the type of packets to be captured (IP packets are captured in this example). Click Next.
- Click Start in order to start the packet capture, as shown here:
- As the packet capture is started, attempt to ping the outside network from the inside network so that the packets that flow between the source and the destination IP addresses are captured by the ASA capture buffer.
- Click Get Capture Buffer in order to view the packets that are captured by the ASA capture buffer.
- The captured packets are shown in this window for both the ingress and egress traffic. Click Save captures in order to save the capture information.
- From the Save Captures window, choose the required format in which the capture buffer is to be saved. This is either ASCII or PCAP. Click the radio button next to the format names. Then, click Save ingress capture or Save egress capture as required. The PCAP files can be opened with capture analyzers, such as Wireshark, and it is the preferred method.
- From the Save capture file window, provide the file name and the location to where the capture file is to be saved. Click Save.
- Click Finish.
This completes the packet capture procedure.
Configure Packet Capture with the CLI
Complete these steps in order to configure the packet capture feature on the ASA with the CLI:
- Configure the inside and outside interfaces as illustrated in the network diagram, with the correct IP address and security levels.
- Start the packet capture process with the capture command in privileged EXEC mode. In this configuration example, the capture named capin is defined. Bind it to the inside interface, and specify with the match keyword that only the packets that match the traffic of interest are captured:
- Similarly, the capture named capout is defined. Bind it to the outside interface, and specify with the match keyword that only the packets that match the traffic of interest are captured:
The ASA now begins to capture the traffic flow between the interfaces. In order to stop the capture at anytime, enter the no capture command followed by the capture name.
Here is an example:
Available Capture Types on the ASA
This section describes the different types of captures that are available on the ASA.
- asa_dataplane - Captures packets on the ASA backplane that pass between the ASA and a module that uses the backplane, such as the ASA CX or IPS module.
- asp-drop drop-code - Captures packets that are dropped by the accelerated security path. The drop-code specifies the type of traffic that is dropped by the accelerated security path.
- ethernet-type type - Selects an Ethernet type to capture. Supported Ethernet types include 8021Q, ARP, IP, IP6, IPX, LACP, PPPOED, PPPOES, RARP, and VLAN.
This example show how to capture ARP traffic: - real-time - Displays the captured packets continuously in real-time. In order to terminate a real-time packet capture, press Ctrl-C. In order to permanently remove the capture, use the no form of this command. This option is not supported when you use the cluster exec capture command.
- Trace - Traces the captured packets in a manner similar to the ASA packet tracer feature.
- ikev1/ikev2 - Captures only Internet Key Exchange Version 1 (IKEv1) or IKEv2 protocol information.
- isakmp - Captures Internet Security Association and Key Management Protocol (ISAKMP) traffic for VPN connections. The ISAKMP subsystem does not have access to the upper-layer protocols. The capture is a pseudo capture, with the physical, IP, and UDP layers combined together in order to satisfy a PCAP parser. The peer addresses are obtained from the SA exchange and are stored in the IP layer.
- lacp - Captures Link Aggregation Control Protocol (LACP) traffic. If configured, the interface name is the physical interface name. This might be useful when you work with Etherchannels in order to identify the present behavior of LACP.
- tls-proxy - Captures decrypted inbound and outbound data from the Transport Layer Security (TLS) proxy on one or more interfaces.
- webvpn - Captures WebVPN data for a specific WebVPN connection.
Caution: When you enable WebVPN capture, it affects the performance of the security appliance. Ensure that you disable the capture after you generate the capture files that are needed in order to troubleshoot.
Defaults
These are the ASA system default values:
- The default type is raw-data.
- The default buffer size is 512 KB.
- The default Ethernet type is IP packets.
- The default packet-length is 1,518 bytes.
View the Captured Packets
On the ASA
Cisco Security Appliance Command Line Configuration Guide ...
In order to view the captured packets, enter the show capture command followed by the capture name. This section provides the show command outputs of the capture buffer contents. The show capture capin command shows the contents of the capture buffer named capin:
The show capture capout command shows the contents of the capture buffer named capout:
Download from the ASA for Offline Analysis

Solved: Cisco ASA 5510 And ASDM. - Cisco Community
There are a couple of ways to download the packet captures for analysis offline:
- Navigate to https://<ip_of_asa>/admin/capture/<capture_name>/pcap on any browser.
Tip: If you leave out the pcap keyword, then only the equivalent of the show capture <cap_name> command output is provided.
- Enter the copy capture command and your preferred file transfer protocol in order to download the capture:
Tip: When you troubleshoot an issue with the use of packet captures, Cisco recommends that you download the captures for offline analysis.
Clear a Capture
In order to clear the capture buffer, enter the clear capture <capture-name> command:
Enter the clear capture /all command in order to clear the buffer for all captures:
Stop a Capture
The only way to stop a capture on the ASA is to disable it completely with this command:
Cisco bug ID CSCuv74549 has been filed to add the ability to stop a capture without completely disabling it and to control when a capture starts to capture traffic.
Verify
There is currently no verification procedure available for this configuration.
Troubleshoot
There is currently no specific troubleshooting information available for this configuration.
Contents
Introduction
This document helps to troubleshoot common problems that occur when you enable intra-interface communications on an Adaptive Security Appliance (ASA) or PIX that operates in software release 7.2(1) and later. Software release 7.2(1) includes the capability to route clear text data in and out of the same interface. Enter the same-security-traffic permit intra-interface command in order to enable this feature. This document assumes the network administrator has either enabled this feature or plans to in the future. Configuration and troubleshooting are provided using the command line interface (CLI).
Note: This document focuses on clear (unencrypted) data that arrives and leaves the ASA. Encrypted data is not discussed.
In order to enable intra-interface communication on ASA/PIX for IPsec configuration, refer to PIX/ASA and VPN Client for Public Internet VPN on a Stick Configuration Example.
In order to enable intra-interface communication on ASA for SSL configuration, refer to ASA 7.2(2): SSL VPN Client (SVC) for Public Internet VPN on a Stick Configuration Example.
Prerequisites

Requirements
Cisco recommends that you have knowledge of these topics:
See More Results
Access lists
Routing
Advanced Inspection and Prevention-Security Services Module (AIP-SSM) Intrusion Prevention System (IPS)—Knowledge of this module is only necessary if the module is installed and operational.
IPS software release 5.x—Knowledge of IPS software is not required if the AIP-SSM is not in use.
Components Used
ASA 5510 7.2(1) and later
AIP-SSM-10 that operates IPS software 5.1.1
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Related Products
This configuration can also be used with the Cisco 500 Series PIX which runs version 7.2(1) and later.
Conventions
Refer to Cisco Technical Tips Conventions for information on document conventions.
Background Information
Note: The IP addressing schemes used in this configuration are not legally routable on the Internet. They are RFC 1918 addresses that have been used in a lab environment.
This table shows the ASA starting configuration:
| ASA |
|---|
Troubleshooting
These sections illustrate several configuration scenarios, related syslog messages, and packet-tracer outputs in relation to intra-interface communications.
Intra-Interface Communications Not Enabled
In the ASA configuration, host 172.22.1.6 attempts to ping host 172.16.10.1. Host 172.22.1.6 sends an ICMP echo request packet to the default gateway (ASA). Intra-interface communications have not been enabled on the ASA. The ASA drops the echo request packet. The test ping fails. The ASA is used to troubleshoot the problem.
This example shows the output of syslog messages and a packet-tracer:
This is the syslog message logged to the buffer:
This is the packet-tracer output:
The equivalent of the CLI commands in ASDM is shown in these figures:
Step 1:
Step 2:
The packet-tracer output with the same-security-traffic permit intra-interface command disabled.
The packet-tracer output drop...implicit rule suggests that a default configuration setting is blocking the traffic. The administrator needs to check the running configuration in order to ensure intra-interface communications are enabled. In this case, the ASA configuration needs intra-interface communications to be enabled (same-security-traffic permit intra-interface).
Intra-Interface Communications Enabled
Intra-interface communications are now enabled. The same-security-traffic permit intra-interface command is added to the previous configuration. Host 172.22.1.6 attempts to ping host 172.16.10.1. Host 172.22.1.6 sends an ICMP echo request packet to the default gateway (ASA). Host 172.22.1.6 records successful replies from 172.16.10.1. The ASA passes the ICMP traffic successfully.
These examples show the ASA syslog message and packet-tracer outputs:
These are the syslog messages logged to the buffer:
This is the packet-tracer output:
The equivalent of the CLI commands in ASDM is shown in these figures:
Step 1:
Step 2:
The packet-tracer output with the same-security-traffic permit intra-interface command enabled.
Note: No access-list is applied to the outside interface. In the sample configuration, the outside interface is assigned security level 0. By default, the firewall does not permit traffic from a low security interface to a high security interface. This might lead administrators to believe that intra-interface traffic is not permitted on the outside (low security) interface without permission from an access-list. However, the same interface traffic passes freely when no access-list is applied to the interface.

Intra-Interface Enabled and Traffic Passed to the AIP-SSM for Inspection
Intra-interface traffic can be passed to the AIP-SSM for inspection. This section assumes the administrator has configured the ASA to forward traffic to the AIP-SSM and the administrator knows how to configure IPS 5.x software.
At this point the ASA configuration contains the previous sample configuration, intra-interface communications are enabled, and all (any) traffic is forwarded to the AIP-SSM. IPS signature 2004 is modified to drop echo request traffic. Host 172.22.1.6 attempts to ping host 172.16.10.1. Host 172.22.1.6 sends an ICMP echo request packet to the default gateway (ASA). The ASA forwards the echo request packet to the AIP-SSM for inspection. The AIP-SSM drops the data packet per the IPS configuration.
These examples show the ASA syslog message and packet-tracer output:
This is the syslog message logged to the buffer:
This is the packet-tracer output:
It is important to note that administrators should use as many troubleshooting tools as possible when they research a problem. This example shows how two different troubleshooting tools can paint different pictures. Both tools together tell a complete story. The ASA configuration policy permits the traffic but the IPS configuration does not.
Intra-Interface Enabled and Access Lists Applied to an Interface
This section uses the original sample configuration in this document, intra-interface communications enabled, and an access-list applied to the tested interface. These lines are added to the configuration. The access-list is intended to be a simple representation of what might be configured on a production firewall.
Host 172.22.1.6 attempts to ping host 172.16.10.1. Host 172.22.1.6 sends an ICMP echo request packet to the default gateway (ASA). The ASA drops the echo request packet per the access-list rules. The host 172.22.1.6 test ping fails.
These examples show ASA syslog message and packet-tracer output:
This is the syslog message logged to the buffer:
This is the packet-tracer output:
Refer to packet-tracer for more information on the packet-tracer command.
Note: In the event the access-list applied to the interface includes a deny statement, the output of the packet-tracer changes. For example:
The equivalent of the above CLI commands in ASDM is shown in these figures:
Step 1:
Step 2:
The packet-tracer output with the same-security-traffic permit intra-interface command enabled and the access-list outside_acl extended deny ip any any command configured to deny packets.
Cisco Asdm 7.2 For Asa 55104
If intra-interface communications are desired on a particular interface and access-lists are applied to the same interface, the access-list rules must permit the intra-interface traffic. With the use of the examples in this section, the access-list needs to be written as:
Cisco Asdm 7.2 For Asa 5510 Software
The equivalent of the above CLI commands in ASDM is shown in these figures:
Step 1:
Cisco Adaptive Security Device Manager (ASDM)
Step 2:
The packet-tracer output with the same-security-traffic permit intra-interface command enabled and the access-list outside_acl extended deny ip any any command configured on the same interface where intra-interface traffic is desired.
Cisco Asdm 7.2 For Asa 5510 Driver
Refer to access-list extended and access-group for more information on the access-list and access-group commands.
Intra-Interface Enabled with Static and NAT
This section explains a scenario where an inside user is trying to access the internal Web server with its public address.
In this case, the client at 192.168.100.2 wants to use the public address of the WWW server (for example, 172.20.1.10). The DNS services for the client are provided by the external DNS server at 172.22.1.161. Because the DNS server is located on another public network, it does not know the private IP address of the WWW server. Instead, the DNS server knows the WWW server mapped address of 172.20.1.10.
Here this traffic from the inside interface has to be translated and re-routed through the inside interface to reach the WWW server. This is called hairpinning. This can be performed through these commands:
For complete configuration details and more information about hairpinning, refer to Hairpinning with Intra-interface communication.
Access-List Forward Thinking
Not all firewall access policies are the same. Some access policies are more specific than others. In the event intra-interface communications are enabled and the firewall does not have an access-list applied to all interfaces, it might be worth adding an access-list at the time intra-interface communications are enabled. The applied access-list needs to permit intra-interface communications as well as maintain other access policy requirements.
This example illustrates this point. The ASA connects a private network (inside interface) to the Internet (outside interface). The ASA inside interface does not have an access-list applied. By default, all IP traffic is permitted from the inside to outside. The suggestion is to add an access-list that looks something like this output:
This set of access-lists continue to permit all IP traffic. The specific access-list line(s) for intra-interface communications reminds administrators that intra-interface communications must be permitted by an applied access-list.